Trusted by over 100 of the world's biggest companies






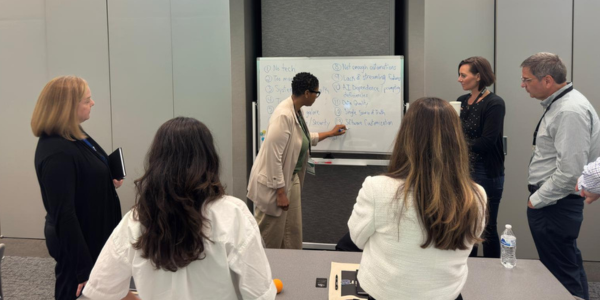
Why operational planning systems require strong governance
Resource management platforms store sensitive information about resource capacity, project planning and organisational performance. Without proper governance controls, organisations risk data exposure and limited visibility into system activity.
How Retain protects enterprise planning environments
Retain provides enterprise-grade security architecture that supports secure deployments across organisations with complex governance requirements.


Retain is proudly SOC 2 Type II and ISO 27001 certified
Retain is SOC 2 Type II and ISO 27001 certifications ensure strong data security. These certifications emphasise our commitment to protecting our customer's data.
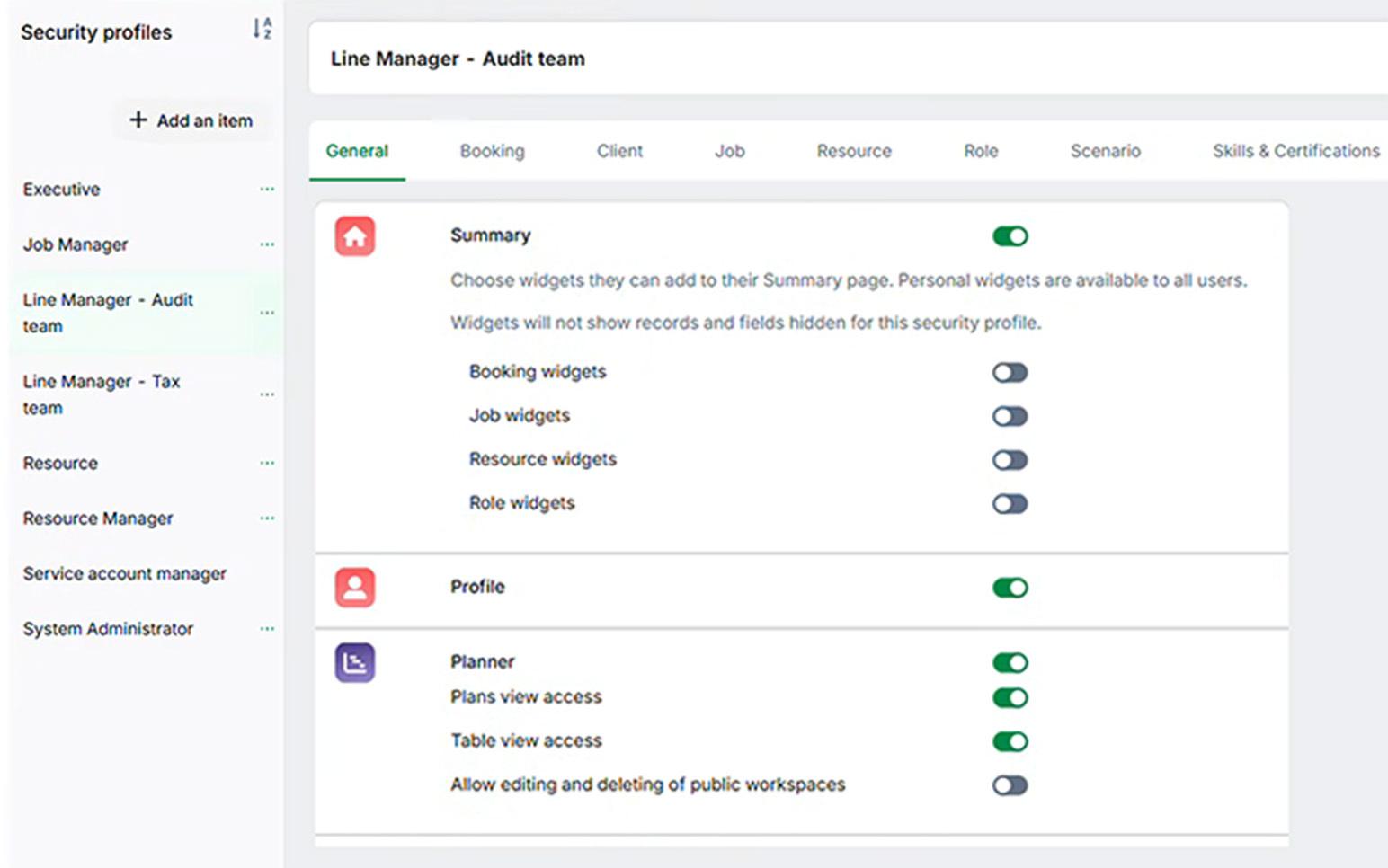
Control access with role-based permissions
Organisations can define user roles and permissions to ensure individuals only access the data relevant to their responsibilities. This supports governance while maintaining operational flexibility across teams.
Track system activity with audit logs
Retain records key system activity across bookings, roles and configuration changes. This provides organisations with visibility into who made changes, when they occurred and how planning data evolves over time.

Secure data across integrations and APIs
Security controls extend across integrations to ensure operational data remains protected when synchronised with external systems and enterprise platforms.
Business Impact
Enterprise security architecture enables organisations to deploy resource management platforms with confidence while maintaining governance and compliance across operations.
Organisations can:

Book Your Demo Today
See how Retain helps you improve utilisation, plan projects with confidence, and deliver work more efficiently.
What security standards should resource management software meet?
Resource management software should meet recognised security standards such as ISO 27001 and SOC 2, while providing role-based access controls, audit logging and secure authentication. These capabilities ensure that operational data is protected and organisations can maintain governance across planning processes.
FAQs
Yes. Retain is ISO 27001 certified, ensuring adherence to internationally recognised information security standards.
Yes. Retain is SOC 2 Type 2 compliant, demonstrating strong controls around data security and operational processes.
Yes. Retain is GDPR-ready and supports organisations managing personal data across regulated environments.
Retain uses role-based permissions to ensure users only access relevant information.
Yes. Audit logs provide visibility into system changes and operational activity.